# Security groups
Security groups act as virtual firewalls that control inbound and outbound traffic to your instances. Our 3 nodes will need to open up connection ports for SSH access, and for each of the 4 network layers to communicate over.
#### Create a Security Group[](https://docs.constellationnetwork.io/sdk/guides/deploy-a-metagraph/security-groups#create-a-security-group)
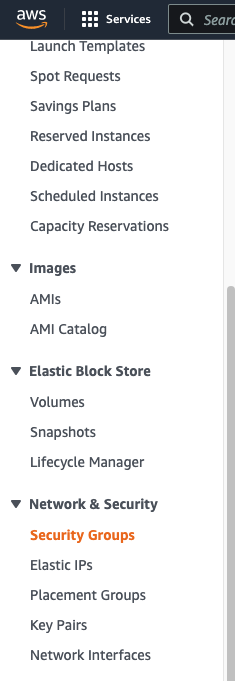
First, navigate to the **`Security Groups`** section in the Amazon [EC2 console](https://us-west-2.console.aws.amazon.com/ec2/home).
**Click on `Create Security Group`**[****](https://docs.constellationnetwork.io/sdk/guides/deploy-a-metagraph/security-groups#click-on-create-security-group)
Create a new security group and provide a name, for example `MetagraphSecurityGroup`.
**Add Inbound Rules**[****](https://docs.constellationnetwork.io/sdk/guides/deploy-a-metagraph/security-groups#add-inbound-rules)
Inbound rules define which ports accept inbound connections on your node. We will need to open up ports for SSH access and for each of the metagraph layers.
Click **`Add Rule`** under the **`Inbound Rules`** section and add the following rules:
| Type | Protocol | Port Range | Source | Purpose |
| ---------- | -------- | ---------- | --------- | ---------- |
| SSH | TCP | 22 | 0.0.0.0/0 | SSH access |
| Custom TCP | TCP | 9000-9002 | 0.0.0.0/0 | gL0 layer |
| Custom TCP | TCP | 9100-9102 | 0.0.0.0/0 | mL0 layer |
| Custom TCP | TCP | 9200-9202 | 0.0.0.0/0 | cL1 layer |
| Custom TCP | TCP | 9300-9302 | 0.0.0.0/0 | dL1 layer |
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://docs.constellationnetwork.io/metagraph-development/guides/deploy-a-metagraph/security-groups.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.